OpenSSL versions
The receipt validation code normally depends on OpenSSL 1.0 and higher. Plus, the code needs to be statically or dynamically linked. This guide describes how to prepare a Xcode project to use the OpenSSL static library.
If you want to use a specific version of OpenSSL:
- you MUST generate the validation code on the command line.
- you MUST pass the option
--openssl-versionon the command line with one of the following value: 1.0 or 1.1.
To check that the generated validation code is compatible with your version of OpenSSL, check the top of the file. The supported OpenSSL version is specified.
OpenSSL Licensing
The use of OpenSSL when linking statically requires to include these sentences in your application (in the Credits.rtf file for example):
This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/). This product includes cryptographic software written by Eric Young (eay@cryptsoft.com).
OpenSSL Binaries
One particular aspect of the OpenSSL project, is that the binaries are not distributed; only the sources are available.
So far, you have the following options:
- Use the Cocoa pods: execute the command
pod OpenSSLorpod OpenSSL-LET(check out the CocoaPods website for more options). This is the preferred way as it makes the setup easier. - Use the MacPort project: execute the command
sudo port install OpenSSL. - Download a pre-built package.
If you don’t have the time or the resources to build OpenSSL by your own, here is the latest builds of the OpenSSL libraries. The distribution includes the header files and the libcrypto and libssl static libraries, build as universal binaries:
- with the i386, x86_64 architectures for OS X
- wtth the i386, x86_64, armv7, armv7s and arm64 architectures for iOS
OpenSSL 1.0.1 (Supported)
- OpenSSL 1.0.1u for OSX (SHA1: 2bf2f11958419ac9212ee25453eee5eec25a52e1)
- OpenSSL 1.0.1u for iOS (SHA1: 51df1b2d7dcdde9363ca3e30bfdbfb5954750ee7)
OpenSSL 1.0.2 (Supported)
- OpenSSL 1.0.2r for OSX (SHA1: 93a5fed794ed7ea1bf94954147ecb88e850140ea)
- OpenSSL 1.0.2r for iOS (SHA1: 279389b72fb11a6fac302ac445fd249a8402e546)
- OpenSSL 1.0.2s for OSX (SHA1: e6242be43da24d1118999ff9d21eb6257ee27b2f)
- OpenSSL 1.0.2s for iOS (SHA1: 17bc474f7b074825b797c3753c3a3bb8f7b6f2bb)
OpenSSL 1.1.0 (Supported)
- OpenSSL 1.1.0j for OSX (SHA1: 4d2d6c91354d2b95def9169dd5e278b402016039)
- OpenSSL 1.1.0j for iOS (SHA1: 7c13a6b0adf437f37c5cda8af2abda94c0d19880)
- OpenSSL 1.1.0k for OSX (SHA1: 93665126347467039b0cd3ab4c971c6832e01928)
- OpenSSL 1.1.0k for iOS (SHA1: 22a2227cd189ebbe76a2bb69269dd24d9ec3ed03)
OpenSSL 1.1.1 (Supported)
- OpenSSL 1.1.1b for OSX (SHA1: d8c5810c5dffd258a2c925b75fc6965779caf2b0)
- OpenSSL 1.1.1b for iOS (SHA1: 83805c4f1c57ee214e9758f96d805d36a306c7dc)
- OpenSSL 1.1.1c for OSX (SHA1: 857afe4317c287abf60020cd05a449ca0d7180d6)
- OpenSSL 1.1.1c for iOS (SHA1: 6fc4fedf5372df695ce474cfdceffaba8fe45277)
Configuring Xcode
If you have downloaded a pre-built package, you need to configure your Xcode project in order to have access to the OpenSSL headers/libraries.
Installation
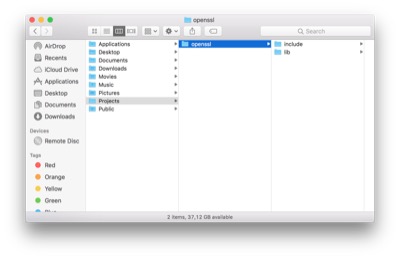
We assume that the pre-built package has been uncompressed in the /Users/Guest/Projects/openssl folder.
The folder should contains an include folder and a lib folder.
Configuration
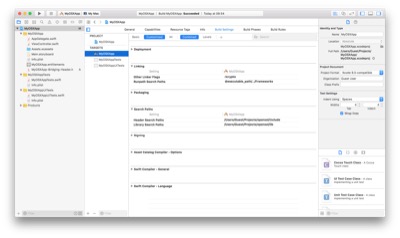
In Xcode:
- Click on the project
- Select the application’s target
- Select the Build Settings tab
- Select the All and Combined filters.
- Add the following values:
- Add
/Users/Guest/Projects/openssl/includeto Header Search Paths - Add
/Users/Guest/Projects/openssl/libto Library Search Paths - Add
-lcryptoto Other Linker Flags
- Add
Specific configuration for Swift
If you are using the Swift generated code, you also need to use a bridging header to import the OpenSSL types and functions. Once the bridging header is created, insert the following in it:
//
// Receigen imports
//
#import <CommonCrypto/CommonDigest.h>
#import <openssl/asn1.h>
#import <openssl/pem.h>
#import <openssl/pkcs7.h>
#import <openssl/sha.h>
#import <openssl/x509.h>
Why OpenSSL ?
From the beginning, Receigen has always used up-to-date code and functions and carefully avoided deprecated APIs, in order to stay fully functional across system upgrades. As the system-bundled OpenSSL shared library is deprecated (since OS X 10.7), Receigen was using the Security framework functions for the receipt parsing and for the cryptographic operations. Unfortunately, using the Security framework has lead to a serie of exploits by offering a way to attack validation code; long story short, the Security framework symbols are vulnerable to runtime injection/swap/swizzling. An attacker can make the application load a shared libraries that will replace some symbols and bypass the various validation checks. In order to prevent this kind of attacks, Receigen is now using a statically linked OpenSSL library for all its cryptographic operations.
Another major reason to switch to OpenSSL was that iOS does not offer enough API to parse and verify the receipt. OpenSSL is therefore the best candidate to provide a robust and cross-platform receipt validation code.